Kubic:kubeadm
What is kubeadm?
kubeadm is a toolkit produced by Kubernetes upstream for the creation and upgrade of Kubernetes clusters
What is Kubernetes?
Kubernetes is an open-source system for automating deployment, scaling, and management of containerised applications. It groups containers that make up an application into logical units for easy management and discovery. Services then receive features like self-healing, high-availability, and load balancing with Kubernetes taking steps to ensure services keep running even in the event of failures. Kubernetes builds upon 15 years of experience of running production workloads at Google, combined with best-of-breed ideas and practices from the community.
Put simply, if you want to run containers across multiple servers in a coordinated way, you probably want to use Kubernetes.
If you only need to run containers on a single server, then we recommend using MicroOS, which offers both the Podman/CRI-O and Docker container runtimes for running containers on a stand-alone system.
Getting Started
Please Note: kubeadm on Kubic is under heavy active development. We are doing our best to keep this guide up to date, but if you notice any anomalies please get in touch or feel free to correct them yourselves.
System installation
First, you need to download a recent installation media of Kubic (x86_64 or AArch64). Any version after 20180815 should work. NOTE: Offical VM images are also available
For installing on bare metal, burn this media to a DVD or USB Stick, and then boot your first system from it. For VMs or VPS providers just boot the image directly. This first system will be the machine we will refer to as the Master, and will run the core Kubernetes services but not any containerised applications. That will be done by additional machines referred to as Nodes.
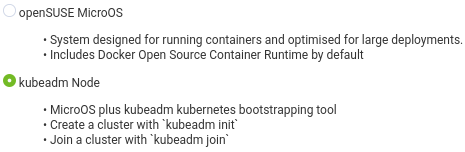
After selecting your language and agreeing to our license, you will be presented with the following "System Roles" screen. Select kubeadm Node
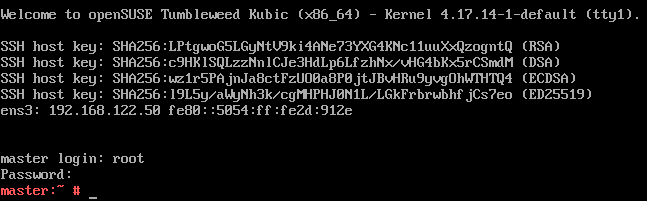
Follow the next step of setting a root password, and if you wish you can customise networking and other options before starting the installation. We recommend leaving the defaults unless you know what you're doing. The installation will then proceed, and you will end up with the following login prompt.
Setting up Kubernetes master
Login using the root password set during the installation. We recommend using ssh to login to the machine remotely, as it will likely simplify things like copy-and-pasting between machines needed later.
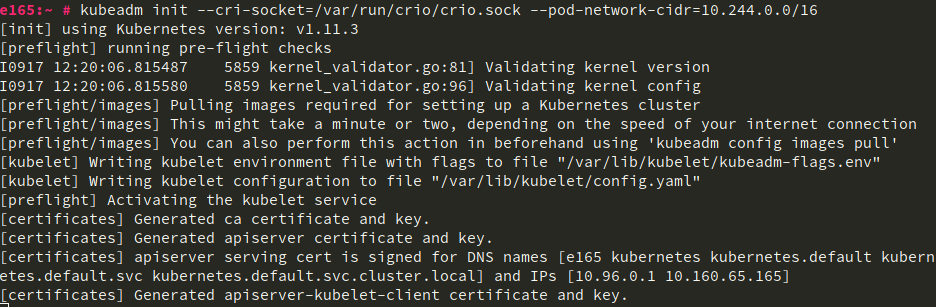
Now run kubeadm init
NOTE: The --pod-network-cidr=10.244.0.0/16 parameter needs to be added if you wish to use the flannel networking interface (aka CNI). That parameter is not needed if you want to use Cilium or our recommended Weave network plugins.
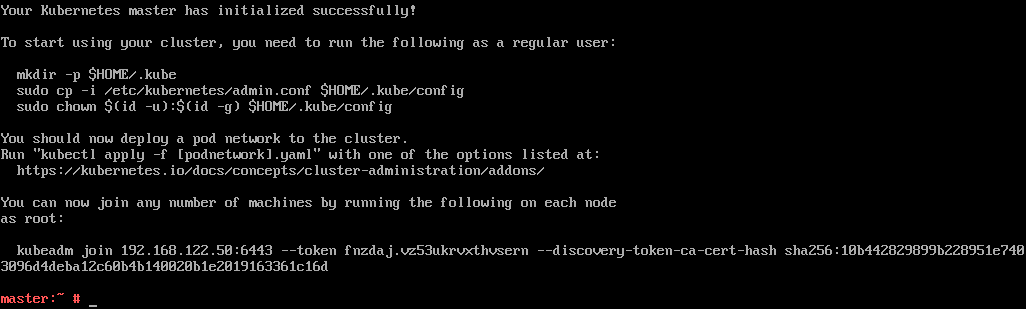
After a brief period, your Master should now be initialised.
Take a note/copy of the line beginning with kubeadm join. You are going to need it to join Nodes to your cluster.
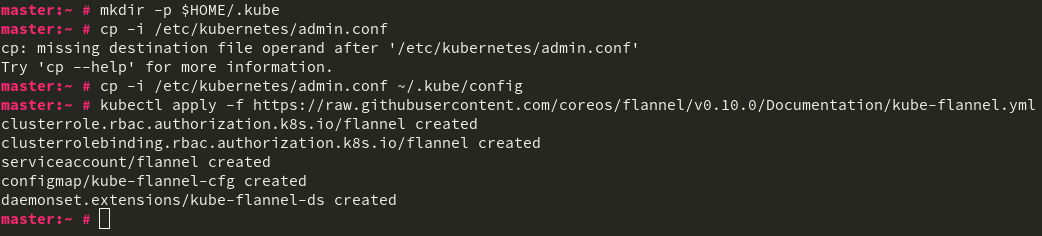
As mentioned in the success message, configure the root user to be able to talk to the cluster by running mkdir -p ~/.kube, then cp -i /etc/kubernetes/admin.conf ~/.kube/config
Setting up the network plugin
The next step is to set up the network plugin. There are three of them to choose and which are tested on Kubic. For now, you can choose only one of them. Weave is our recommended for most basic use cases.
Weave
Weave provides simple, resilient multi-host containers networking.
Setup weave by running kubectl apply -f /usr/share/k8s-yaml/weave/weave.yaml
Flannel
Warning: flannel used to be our recommended CNI plugin but is now considered unstable. This documentation is here for legacy reference purposes
Flannel is a simple network provider. It has less features and does not provide Network Policies, but it was always supported in Kubic.
You can setup flannel by running kubectl apply -f /usr/share/k8s-yaml/flannel/kube-flannel.yaml
You may need to reboot the master after applying this change if you see runtime network not ready: NetworkReady=false reason:NetworkPluginNotReady message:Network plugin returns error: Missing CNI default network when runnnig kubectl describe nodes.
Joining nodes to the cluster
This now means your master is fully set up and ready for other nodes to join it. You install them the same way as your Master, selecting the kubeadm Node role just as before.
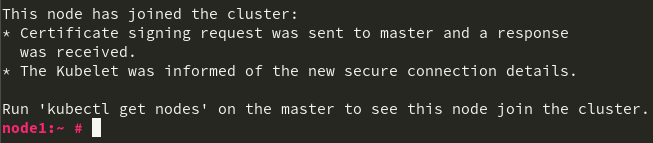
However, unlike on your master, you run the kubeadm join command by pasting the line that was presented at the end of the kubeadm init run from the Master.
After a short run, you should get the following confirmation that your node has joined the cluster.
Verifying the cluster
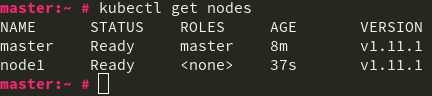
Now from your master node (or any system with kubectl installed and the /etc/kubernetes/admin.config file from the master copied to your users $HOME/.kube/config file) you can run kubectl get nodes to confirm your cluster is operational.
Congratulations! You now have a working Kubernetes cluster.
Single Master Operation
You may wish to experiment with Kubernetes as a single master. To achieve this you need to untaint the master to allow pods to be scheduled on the master.
kubectl taint nodes --all node-role.kubernetes.io/master-
Further Documentation
For further documentation, we highly recommend you read the upstream kubeadm documentation which we aim for Kubic to be compatible with.